
Interoperability in Practice: One Credential, Many Verifiers, Zero Vendor Lock-In
The dream of reusable digital identity dies quietly — not in a breach, but the first time a user presents a perfectly valid credential and the verifier rejects it. No fraud was committed. No policy was violated. The system simply never agreed on a common language with the issuer.
This is the operational failure most architects discover too late. "Verify once, reuse everywhere" only holds if credential formats, presentation protocols, and trust resolution share a common foundation. Without standards alignment at every layer, you have not built portable credentials. You have built a slightly more private version of the same fragmented digital identity problem you set out to solve.
The promise of Zero-Knowledge KYC. It is not just about data minimization — it is about building digital credentials that work across verification systems, across regulated industries, and across time. Every redundant identity verification loop drives up verification costs and undermines user privacy for users moving between different services.
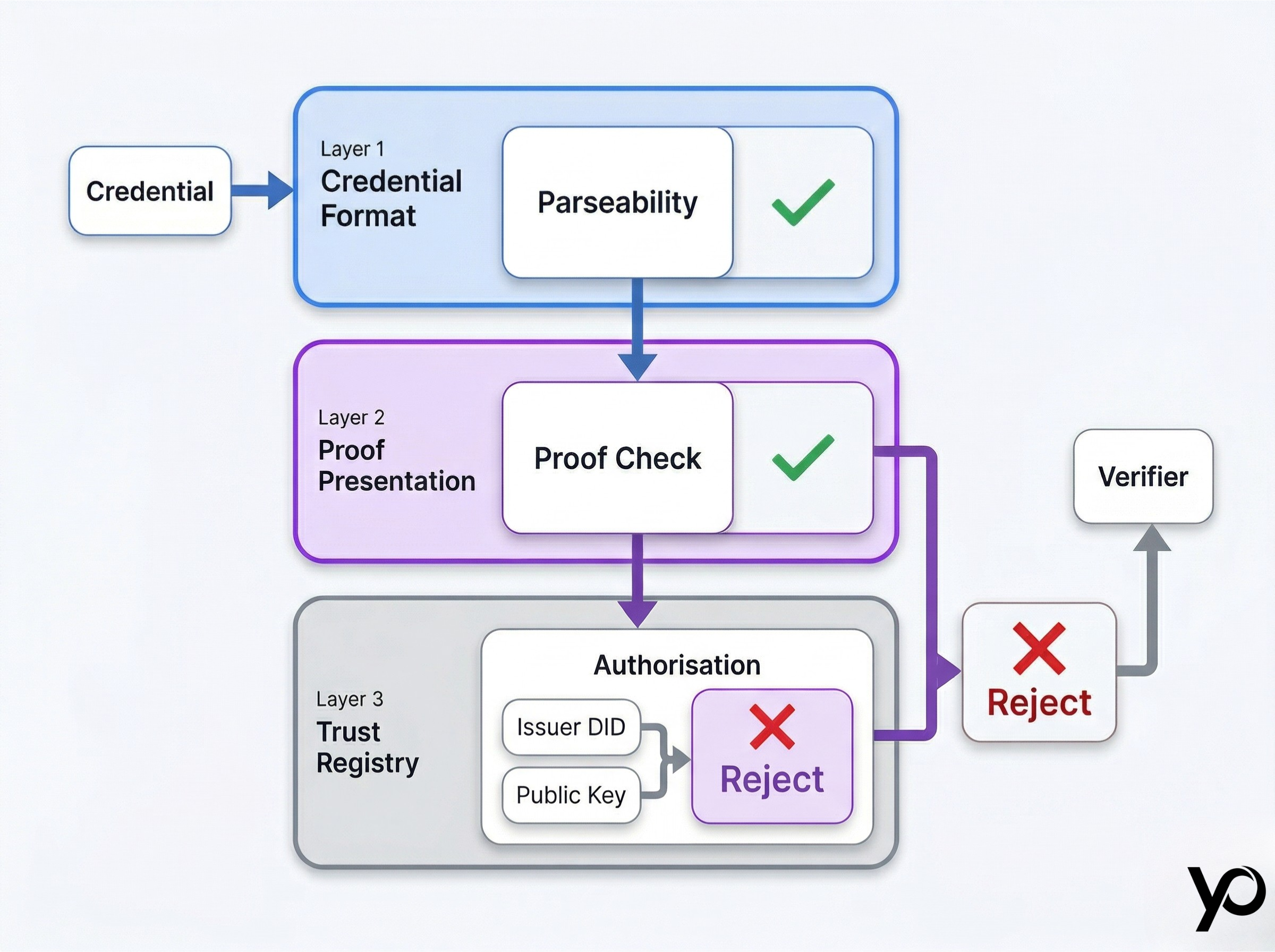
The 30-Second Map: Three Layers Where Interoperability Must Hold
Interoperability is not a single property. It is a stack. A credential can be syntactically valid and still fail if any one layer is misaligned.
Layer one: credential format. The credential must be structured in a way that any compliant verifier can parse — standard encoding and a data model that does not depend on a proprietary SDK to read.
Layer two: proof presentation. When a holder presents a credential, the presentation itself must be in a format the verifier accepts. This is where most production failures happen — not because the credential is wrong, but because the verifier expects JWT-VC and the wallet sends JSON-LD.
Layer three: trust registry. The verifier must resolve whether the issuer was authorised to issue the credential. If trust is hardcoded — a public key embedded in the verifier's configuration — the whole system breaks the moment the issuer rotates that key.
Where the model breaks. The issuer–holder–verifier model works in theory. Vendor lock-in enters through any one of these three layers. An issuer using proprietary systems forces any verifier that wants to accept those credentials to integrate directly with that issuer's SDK and absorb every breaking change they ship.
Digital Identity: Why Vendor Lock-In Starts Earlier Than You Think
Most teams do not realise they are building vendor lock-in until they are already inside it.
The bilateral integration trap. When an issuer builds a custom credential schema and a verifier builds a custom parser for it, they have created a bilateral dependency. Add ten issuers and ten verifiers and you have one hundred integration points. This is the N×M combinatorial explosion that makes scaling any real-world digital identity ecosystem impractical without shared standards.
The operational cost that compounds. Each bilateral integration requires maintenance. Every schema update, every SDK version bump, every key rotation becomes a coordination event between two teams. Verification costs scale with the number of parties — not the complexity of the task. In regulated sectors, maintaining N×M relationships becomes a structural barrier to market entry and drives up customer onboarding costs.
The failure mode for users. When a user moves between different services — a DeFi exchange, a fintech wallet, an RWA marketplace — they expect their verified digital identity to travel with them. If each service has its own issuer relationship and its own credential format, the user re-verifies every time. That is not a user experience problem. It is an architectural failure that also raises compliance violations risk across isolated systems.
Identity Verification: The W3C Standards That Actually Ship
The World Wide Web Consortium (W3C) has produced the specifications that make vendor-independent identity verification possible. These are implemented and actively used in government and enterprise identity systems across regulated industries today.
W3C Verifiable Credentials: The Data Model
W3C Verifiable Credentials define a standard data model for cryptographically verifiable claims. A verifiable credential contains claims about a subject, a reference to the issuer's identity, an issuance date, and a cryptographic proof that confirms the credential's authenticity. Any party with access to the issuer's public key can verify the credential without contacting the issuer directly. The data structure is standardised so that any compliant implementation can read it — without a proprietary library.
Decentralized Identifiers: The Resolution Layer
Decentralized identifiers (DIDs) solve the resolution problem. A DID is a globally unique identifier that resolves to a DID Document containing the issuer's public keys, service endpoints, and verification methods. By resolving a DID, a verifier discovers the cryptographic material needed to validate any credential issued by that issuer — without a bilateral relationship.
What the data model guarantees — and what it does not. W3C Verifiable Credentials do not guarantee interoperability by themselves. They guarantee a common structure — a shared vocabulary for issuer, subject, claim, and proof — that any compliant implementation can read. The actual interoperability comes from disciplined use of that standard in combination with shared credential schemas and common proof formats.
World Wide Web Consortium compliance as a long-term commitment. A system that issues "VC-inspired" credentials with proprietary extensions is not standards-compliant. True compliance means the credential can be instantly verified by any conformant wallet or verifier — regardless of who built it. World Wide Web Consortium compliance is a commitment, not a checkbox.
Data Model: The Contract Between Issuers and Verifiers
A credential schema defines the structure and vocabulary of a credential — which fields are present, their data structure, and what they mean. When issuers and verifiers share a schema, a credential issued by one party can be verified by any other party that knows the schema — without prior coordination.
The schema registry pattern. In production identity systems, schemas are published to a shared, versioned registry — either on-chain or via a well-known HTTPS endpoint. Verifiers resolve schemas by URI, not by contacting the issuer. This decouples the verifier's runtime from the issuer's infrastructure, supporting offline credential verification even when the issuer's systems are down.
Versioning is not optional. Credential schemas must be versioned. When an issuer needs to add a field, change a type, or deprecate an attribute, they publish a new schema version. Breaking changes should never be deployed silently against a mutable schema URI.
The schema management failure mode. A schema published without versioning, or one that lives at a mutable URL, becomes a fragility point. When the issuer changes the schema in place, every verifier that has cached it breaks silently — not a cryptographic failure but an implementation details failure that propagates across the entire ecosystem.
Decentralized Credentials: Eliminating Bilateral Trust
Traditional systems require every relying party to register with every identity provider, exchange certificates, and maintain bilateral relationships. This does not scale to a world where hundreds of issuers serve thousands of verifiers across public services and regulated industries simultaneously.
How DID Resolution Replaces Directory Lookups
Decentralized identifiers solve this by replacing directory lookups with cryptographic resolution. When a credential is cryptographically signed by an issuer whose identity is expressed as a DID, any verifier anywhere can resolve that DID, retrieve the public key, verify the cryptographic signature, and confirm the credential issued — without any prior relationship with the issuer. This eliminates isolated systems that can only communicate with pre-registered partners.
Choosing a DID method in production. did:web is simple but depends on DNS and TLS. did:key works offline but cannot be updated. did:ethr provides on-chain key rotation but introduces blockchain dependencies. For production identity systems in regulated environments, the choice of DID method is a security and availability decision.
The correlation risk with persistent identifiers. Using the same DID across multiple verifiers enables cross-verifier correlation — a privacy failure that undermines data minimization. In Zero-Knowledge KYC architectures, holders should use pairwise DIDs or ephemeral identifiers. The credential payload carries the claim. The identifier does not need to be permanent.
Identity Systems: Understanding Proof Formats
Even when two parties agree on the W3C Verifiable Credentials data model and the same credential schema, they may still fail to interoperate at the proof layer. The cryptographic signature format determines which verifiers can validate a credential.
JWT-VC: The Widely Supported Default
JWT-VC encodes the credential as a JSON Web Token. It is widely supported, easy to validate with standard libraries, and the default choice for most enterprise identity systems. Its limitation is that it does not natively support selective disclosure without additional mechanisms.
JSON-LD With LD-Proofs: Richer but More Complex
JSON-LD with LD-Proofs embeds the proof directly in the JSON-LD document using a linked data signature scheme. JSON-LD credentials can support selective disclosure through BBS+ signatures, allowing a holder to prove a subset of attributes without revealing the full credential. The trade-off is higher complexity and less uniform library support across identity systems.
SD-JWT: The Emerging Standard for Data Minimization
SD-JWT adds selective disclosure capabilities to standard JWT-VC. The issuer signs individual claims separately, and the holder chooses which claims to disclose in any given verifiable presentation. SD-JWT is being adopted in the European Digital Identity Wallet (EUDIW) framework as the recommended format for new deployments that require data minimization by default.
Supporting multiple formats in production. No single format wins everywhere. Production verifiers should accept at least two formats — typically JWT-VC and SD-JWT — to ensure digital credentials from different identity providers can be instantly verified without forcing re-issuance. Verifying credentials from multiple issuers requires this format flexibility.
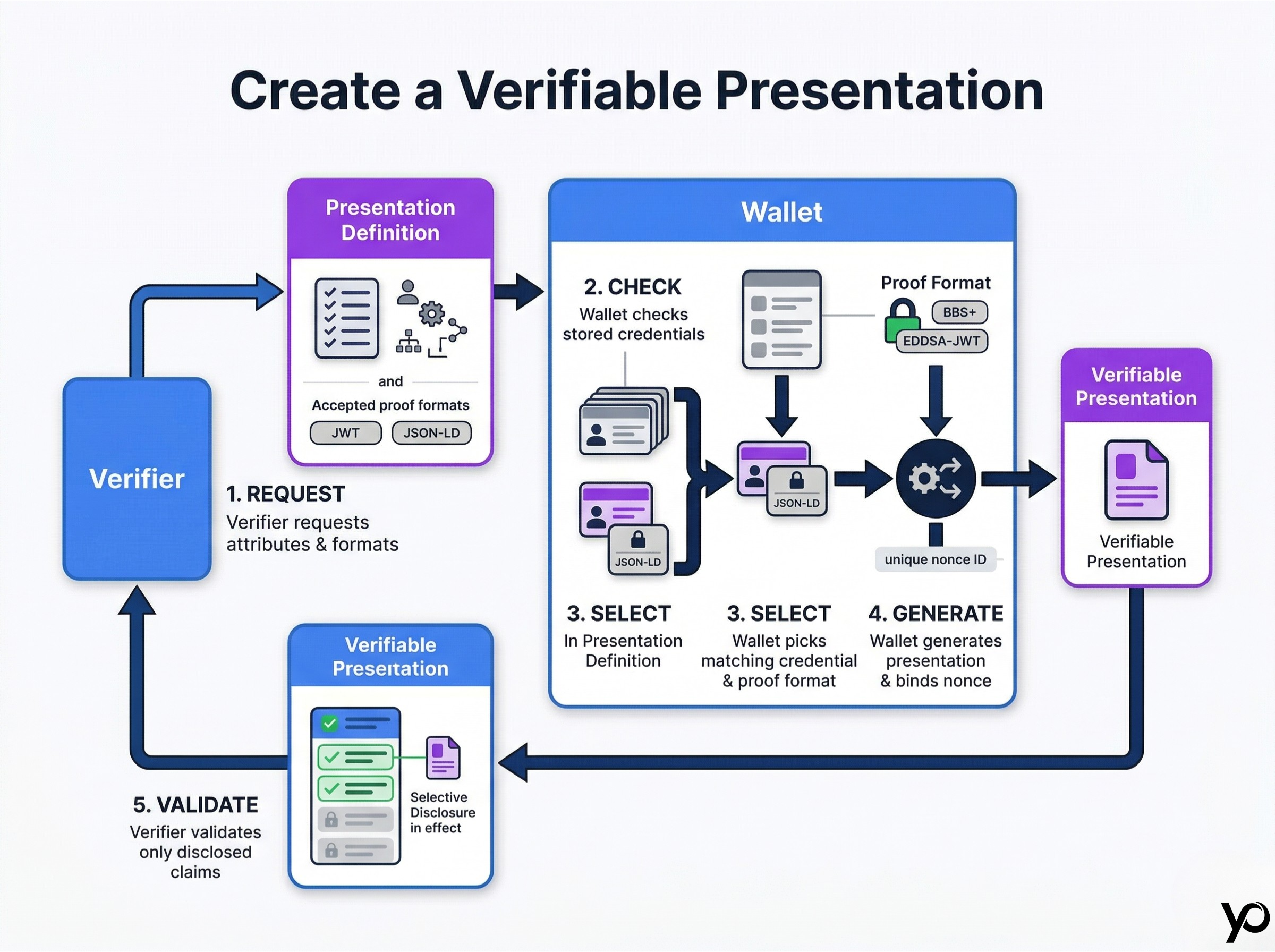
Cryptographic Proof: How Proof Format Negotiation Works
When a holder presents a credential, the verifier must signal which proof formats it accepts. The holder's digital wallet selects the appropriate format and generates a verifiable presentation accordingly.
The Presentation Exchange Protocol
OpenID for Verifiable Presentations (OID4VP) defines a standard mechanism for this negotiation. The verifier sends a Presentation Definition specifying credential types and proof formats it requires. The wallet evaluates its stored credentials, selects the ones that match, and generates a verifiable presentation — a wrapper containing the selected credential, the holder's cryptographic signature over the nonce, and the chosen proof format. This process is what makes credential verification both secure and interoperable.
Selective Disclosure in Action
Suppose a financial services verifier only needs to know that a user is over 18 and has passed AML screening. The Presentation Definition requests those two attributes specifically. The holder's personal digital wallet generates a proof that reveals only those claims — using SD-JWT selective disclosure or a zero knowledge proofs-based predicate — without exposing sensitive data like name, address, or document number. The verifier gets instantly confirmed results. The underlying data never leaves the holder's control.
The format negotiation failure mode. If a verifier's Presentation Definition requires SD-JWT but the wallet only holds a JSON-LD credential, the presentation fails. This is not a credential validity failure — it is a format negotiation failure. The fix is to issue credentials in multiple formats from the start, or ensure your acceptance infrastructure handles format translation where standards permit.
Interoperability Protocols: The Trust Registry Layer
Knowing that a credential is cryptographically valid tells you it has not been tampered with. It does not tell you whether the issuer was authorised to issue it. A cryptographically signed credential from an unauthorised issuer is a forgery — even if cryptographic verification passes.
What a trust registry is. A trust registry answers: "Is this issuer permitted to issue this type of credential?" It maps issuer DIDs to the credential types they are authorised to issue, the jurisdictions they operate in, and their current status. Compliance workflows that depend on trust registries are auditable, repeatable, and scalable in ways that bilateral agreements are not.
Open Registries and Government Adoption
The eIDAS 2.0 regulation mandates that EU member states operate trusted issuer registries for the European Digital Identity Wallet. These registries are publicly accessible and governed by government mandates. Any government agency across the EU can accept credentials from any EU-authorised issuer — without bilateral agreements. This is what government adoption of open standards looks like in practice.
Permissioned Registries for Regulated Sectors
In financial services, healthcare, and other regulated sectors, trust registries are often permissioned — managed by a consortium, regulator, or sector body. Verifiers integrate with the registry once and inherit trust in all listed issuers. This is the correct architecture for regulated industries that need strict control over accepted identity providers, while still avoiding compliance violations from siloed integrations.
The hardcoded key anti-pattern. Many early deployments skip the registry layer entirely and hardcode the issuer's public key directly into the verifier. When the issuer rotates their private key — which they must do on a regular security schedule — every verifier that hardcoded the old key breaks silently. A single key rotation becomes a multi-team emergency. Connecting to a trust registry from day one eliminates an entire category of production failure.
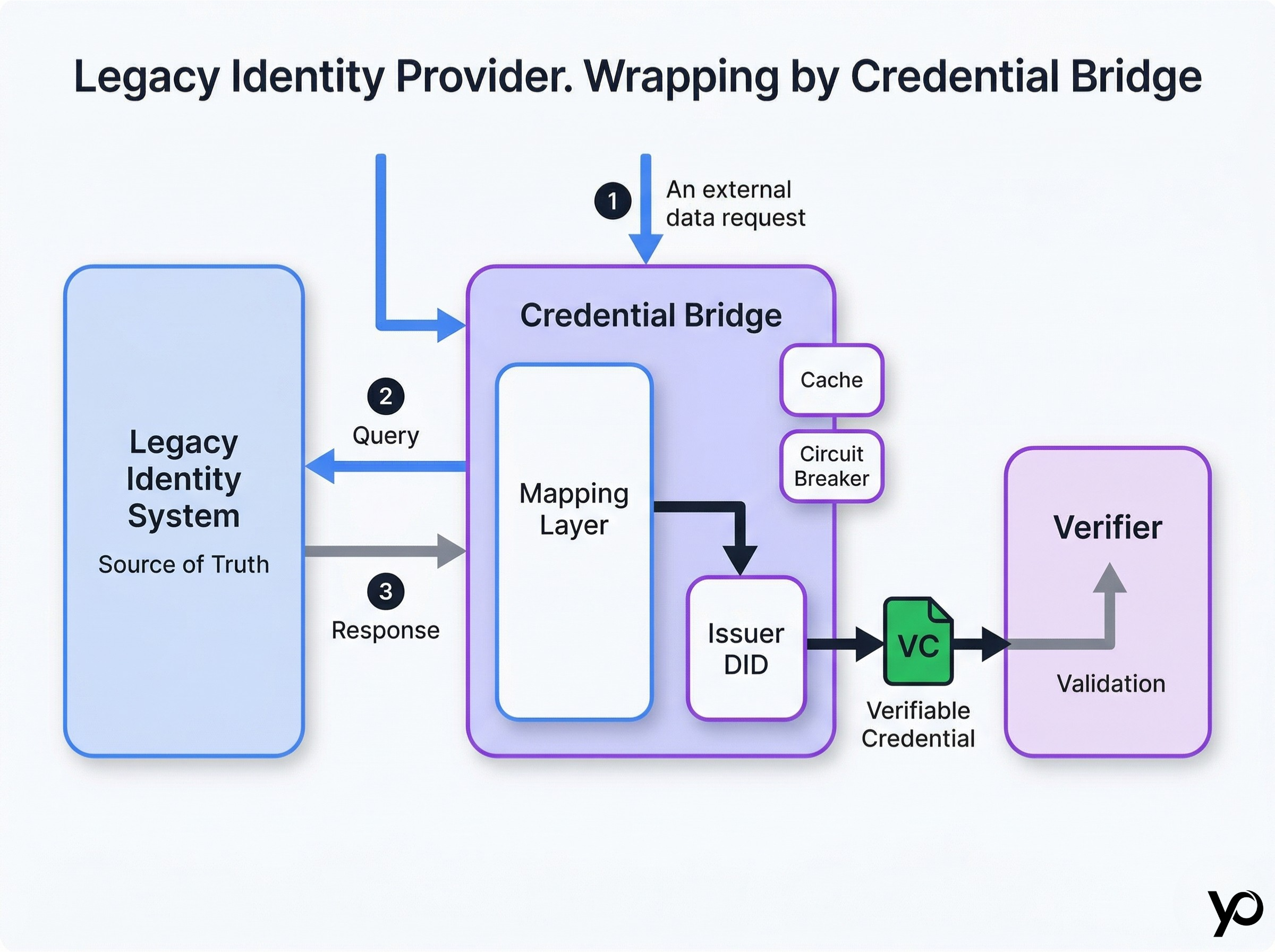
Existing Systems: Integrating Legacy Infrastructure
Most organisations are not starting from scratch. They have existing identity systems — LDAP directories, OAuth 2.0 servers, SAML federations, on-premise KYC databases — that cannot be replaced overnight. Interoperability in practice means bridging these legacy systems to modern standards without creating a brittle dependency chain.
The Credential Bridge Pattern
A credential bridge is a service that wraps a legacy identity provider and issues W3C Verifiable Credentials on its behalf. The legacy system remains the source of truth. The bridge translates queries into the legacy system's protocol, receives responses, and wraps the results in a standards-compliant verifiable credential signed with the bridge's issuer DID. From the verifier's perspective, the credential is indistinguishable from one issued natively.
Risks of the adapter pattern. If the bridge becomes a single point of failure, the legacy system's availability profile propagates to the new credential infrastructure. Design the bridge with independent caching, circuit breakers, and fallback behaviour. Ensuring direct access to the underlying data from a secondary path is a business continuity requirement. Access control at the bridge layer matters too — a single system account with broad read access to sensitive data limits scoped access and widens the blast radius of a compromise.
Managing operational costs long term. Every schema update in the legacy system requires a corresponding update to the bridge mapping. The long-term strategy should be to migrate source-of-truth data to a system that can issue W3C Verifiable Credentials natively — but that migration does not need to happen before the credential infrastructure goes live.
Digital Wallet: Supporting Multiple Credentials and Identity Providers
A digital wallet is where credentials live — a secure store that holds verifiable credentials from multiple identity providers and presents the right one to the right verifier at the right time.
The multi-issuer wallet requirement. A user might hold a government-issued mobile driver's license credential, a KYC credential from a financial services provider, and a professional certification issued by an industry body — all in the same personal digital wallet. Each was issued by a different identity provider, in potentially different formats, under different trust registries. The wallet must manage all of them coherently.
Credential selection logic. When a verifier sends a Presentation Definition, the wallet evaluates all stored credentials and selects the best match: a credential from an issuer trusted by the verifier, in a format the verifier accepts, covering the attributes required, with a valid revocation status. Wallets that implement this logic correctly make interoperability invisible to the user — digital credentials are instantly verified without manual selection.
The same-entity problem. A user may hold multiple digital credentials that all refer to the same natural person — issued by different identity providers at different times. Linking these without creating a global identifier that enables cross-verifier tracking is a core design challenge. Use zero knowledge proofs to prove a binding without revealing the linking identifier, protecting the rightful owner's privacy.
Offline verification as a business continuity requirement. A digital wallet must be able to present credentials and a verifier must be able to verify them without a live network connection. A border agent verifying a mobile driver's license at a remote crossing cannot depend on a cloud revocation oracle. Offline verification requires embedding status information in the credential at issuance time — not as an afterthought.
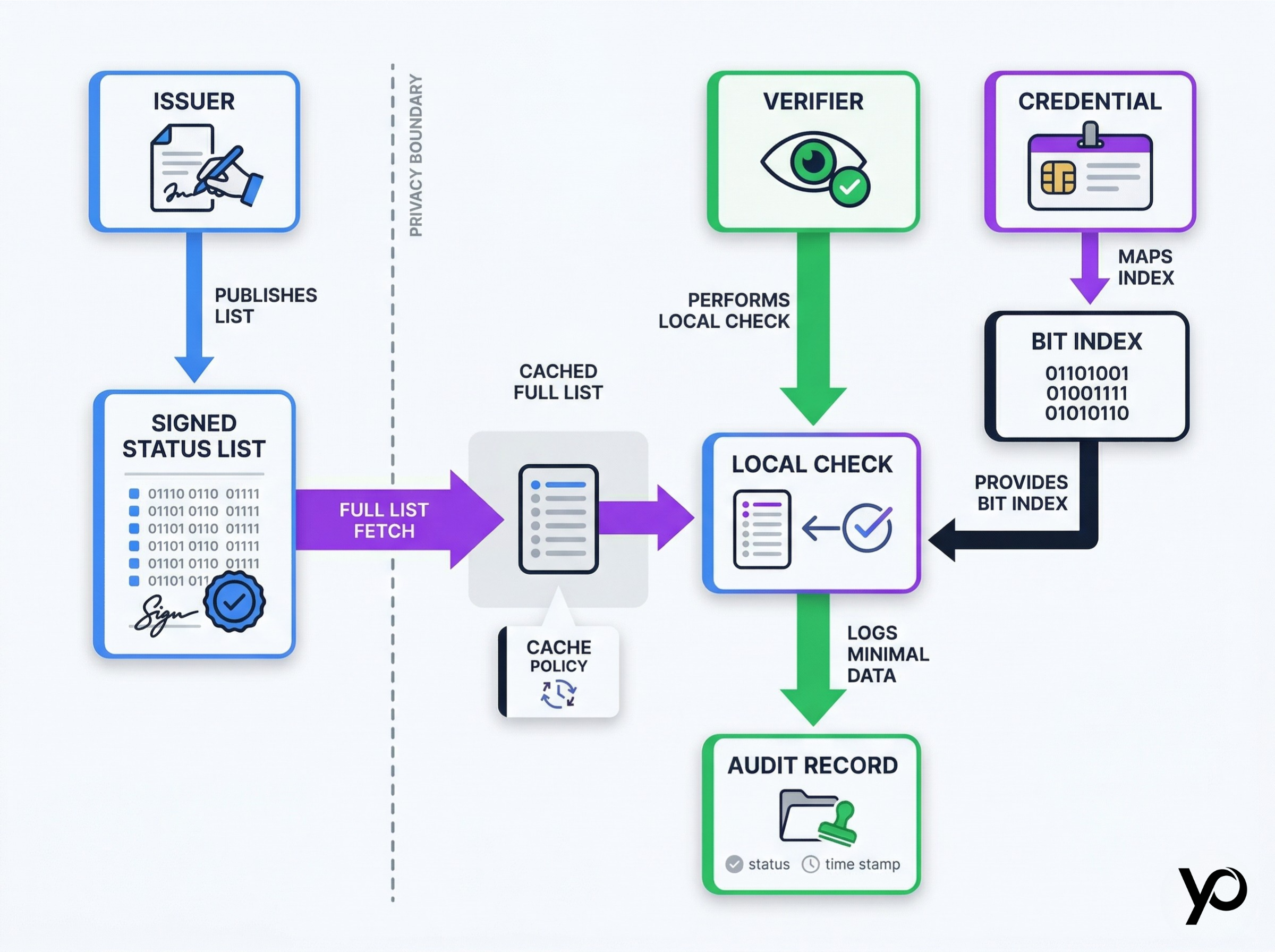
Data Integrity: Revocation Without Privacy Violation
A verifiable credential is only as trustworthy as its current status. A credential that was valid when issued may have been revoked — because the underlying identity verification was fraudulent, or because the credential expired. Verifiers need to check status without enabling issuers to track usage patterns and detect anomalies in user behaviour.
The Status List Pattern
W3C Bitstring Status List defines a standard mechanism for credential revocation that protects holder privacy. The issuer publishes a bitstring — a long array of bits, each corresponding to a credential by index. Verifiers download the full status list and check the relevant bit locally. The issuer never learns which credential was checked, by whom, or when. This is how to ensure interoperability in revocation without surveillance.
Revocation freshness and caching policy. A verifier that caches a status list for 24 hours may accept a credential revoked 23 hours ago. Define explicit freshness policies for each credential type. Stale verified data is a compliance violation waiting to be discovered in an audit. In financial services, freshness windows are typically short; in lower-risk contexts, daily refreshes may be sufficient.
Data integrity under key rotation. Status lists are cryptographically signed by the issuer. When the issuer rotates their signing private key, they must re-sign the status list and publish both the new signature and an overlap window during which the old key remains valid. Verifiers that cache the old signature must detect the transition and re-validate. This interaction between key management and revocation infrastructure is one of the most overlooked operational dependencies in production credential systems.
What the compliance audit record must contain. Compliance audits require a verifier to demonstrate what credential it accepted, from which issuer, under which schema version, at what point in time — without storing the credential payload or any personal data. The evidence record is: timestamp, issuer DID, schema URI, policy version, allow/deny decision. These compliance workflows must be designed from day one.
Fraud Prevention: Where Interoperability and Security Converge
Interoperability does not weaken security. A credential ecosystem built on open standards is significantly more auditable — because every verifier independently performs cryptographic verification against a shared trust registry, enhancing security at the ecosystem level.
Replay attack prevention. A verifiable presentation must include a nonce — a challenge value provided by the verifier — that the holder signs along with the credential. Without a nonce, an attacker who intercepts a valid presentation can replay it to a different verifier. All compliant presentation protocols include nonce binding as a mandatory mechanism.
Issuer impersonation via unresolved DIDs. An attacker can create a fraudulent DID and issue a credential that looks superficially legitimate. If the verifier resolves the DID correctly and checks the trust registry, the fraud is detected. If the verifier only checks the signature and skips the registry lookup, the fraud succeeds. Trust registry validation is not optional for fraud prevention.
Schema injection attacks. A malicious credential may include additional fields not present in the declared schema — fields that a poorly written verifier might evaluate in unexpected ways. Verifiers should validate credentials strictly against the declared schema and reject any credential that contains undeclared fields. This is a future-proof defensive pattern that scales regardless of how schemas evolve.
Zero-knowledge proofs as a structural security advantage. Zero-knowledge proofs add fraud resistance that traditional verification systems cannot match. A holder proves a predicate — "age over 18", "KYC level is tier 2" — without revealing the underlying data. The proof is bound to a specific nonce and verifier identifier and cannot be replayed. This is where Zero-Knowledge KYC creates a structural security advantage over traditional identity verification approaches.
Government Adoption: Real-World Interoperability Patterns
Standards-based credential infrastructure is operational in multiple jurisdictions today, serving public services across borders. Its deployment patterns provide a reference architecture for private sector implementations in regulated industries.
Driver's License: The Mobile Credential Pattern
The ISO 18013-5 standard defines the mobile driver's license (mDL) — a W3C-compatible digital credential that encodes driving licence attributes in a standardised format. Under eIDAS 2.0 and the European Digital Identity Wallet (EUDIW) framework, government mandates require that digital identity credentials be portable across all EU member states. A credential issued by the German government must be verifiable by an Austrian border agency, a Spanish financial institution, or a French healthcare provider — without bilateral agreements.
The Architecture Behind Cross-Border Portability
Each EU member state operates a trust registry listing its authorised credential issuers. Verifiers across the EU resolve issuer DIDs against these registries. Presentation follows the OID4VP protocol. The data model is W3C Verifiable Credentials. No bilateral integrations are required. The architecture scales to 27 member states without N×M complexity — any government agency can instantly confirm a credential issued in another jurisdiction.
Regulated Financial Services: Bridging Legacy and Modern Identity Systems
A tier-1 bank deploying Zero-Knowledge KYC across its business units faces a multi-decade installed base of legacy identity systems — SAML providers, on-premise KYC databases, third-party AML screening vendors. The practical architecture uses credential bridges combined with a central trust registry operated by the compliance function. New verifiers connect to the registry and inherit trust in all vetted issuers without additional procurement. Verification costs per new service integration drop from months to days.
Healthcare and Education: Patient Records and Educational Credentials
Patient records, educational credentials, and professional certifications share a common challenge: they are long-lived, issued by many organisations, and need to be verifiable by parties with no prior relationship to the original issuer. With W3C Verifiable Credentials and a trust registry listing authorised issuers, a hospital can verify the rightful owner of a medical professional's credential from a national medical council without any integration work. Regulatory compliance is maintained end-to-end without centralising sensitive data.
What Matters vs What Is Noise
| Decision | What Matters | What Is Noise |
|---|---|---|
| Credential format | W3C VC data model compliance, schema versioning | Whether the issuer uses their own SDK or a third-party library |
| Proof format | Supporting JWT-VC + SD-JWT for compatibility | Debating JSON-LD vs JWT as a philosophical position |
| Trust resolution | Live registry lookup at verification time | Cached issuer certificates that "never change" |
| DID method | Offline resolvability, key rotation support | Which blockchain the DID is anchored to |
| Wallet compatibility | OID4VP compliance for presentation | Whether the wallet has a native mobile app |
| Revocation | Status list freshness policy and audit logging | Whether the revocation endpoint uses REST or GraphQL |
What Breaks in Production: Anti-Patterns to Avoid
Every interoperability failure in production traces back to a small number of architectural decisions made earlier.
Hardcoding issuer public keys. The verifier works in staging where the issuer's key never changes. In production, the issuer rotates their key on schedule — and every verifier that hardcoded the old key begins rejecting all credentials silently. The incident coordination takes days. The technical fix takes hours. Use a trust registry.
Single-schema verifier logic. Building a verifier that only accepts one specific credential schema means the verifier must be updated every time the issuer updates their schema. Version your schemas, support the current and previous version simultaneously, and build schema resolution into your verifier runtime.
Revocation without a freshness policy. A verifier that caches status lists indefinitely will eventually accept revoked credentials. Define the maximum age of an acceptable cached status list for each credential type and enforce it at the verifier level. Log every revocation check — not the credential content, but the fact that a check was performed.
Skipping offline verification. Designing for online-only verification means offline never gets built. Build offline support from day one using short-lived embedded status rather than live revocation oracles.
The single-issuer assumption. Starting with a single issuer and deferring multi-issuer support is how vendor lock-in becomes structural. Design your acceptance infrastructure for multiple identity providers from the start.
CTO Checklist: Interoperability Safe Defaults
Use W3C Verifiable Credentials and Decentralized Identifiers as your foundation. Do not build on proprietary formats that cannot be read by a compliant third-party verifier.
Support at least two proof formats in your verifier. JWT-VC and SD-JWT is the recommended combination for new deployments.
Connect to a trust registry before launch. Never hardcode issuer public keys in your verifier configuration.
Publish credential schemas to a versioned, publicly accessible registry. Define a schema versioning policy that includes a deprecation schedule.
Test with credentials from at least two different identity providers before going live. Single-issuer testing hides compatibility failures.
Build for offline verification from day one. Use short-lived credentials with embedded status.
Define and enforce a revocation freshness policy for each credential type. Make this a configuration value that compliance can adjust without a code deployment.
Implement selective disclosure at the presentation layer. Ensure Presentation Definitions request only the attributes required for each verification context — this is data minimization in practice.
FAQ
What is credential interoperability and why does it matter?
Credential interoperability means that a verifiable credential issued by one identity provider can be presented to and verified by any other compliant verifier — without bilateral agreements, custom integrations, or proprietary software dependencies. Without it, every new verifier relationship requires a new integration project, re-issuance of credentials, and verification costs that scale with the number of parties rather than approaching zero.
What is the difference between a DID and a Verifiable Credential?
A Decentralized Identifier (DID) is a globally unique identifier that resolves to a DID Document containing public keys and service endpoints for an entity. A Verifiable Credential is a structured claim about a subject, cryptographically signed by an issuer whose identity is typically expressed as a DID. The DID provides the resolution mechanism. The verifiable credential carries the actual claim — the verified data about the holder.
How does selective disclosure support data minimization?
Selective disclosure allows a holder to prove specific attributes from a credential without revealing the entire credential payload. A user can prove they are over 18 without disclosing their date of birth, protecting user privacy and limiting the sensitive data exposed in every identity verification event. Combined with zero knowledge proofs, selective disclosure enables verification of predicates without revealing the underlying attribute value at all.
What is a trust registry and how does it work?
A trust registry is an authoritative list of identity providers and the credential types they are authorised to issue. When a verifier receives a credential, it checks that the issuer's DID appears in the relevant trust registry with the appropriate authorisation. Verifiers that connect to a registry once inherit trust in all listed issuers automatically — without further coordination. This is how regulatory compliance is enforced across an ecosystem without centralised credential storage.
Can a single digital wallet hold credentials from multiple identity providers?
Yes. A compliant digital wallet can hold credentials from any number of identity providers, in any supported proof format, under any trust registry. When a verifier sends a Presentation Definition, the wallet evaluates all stored credentials and selects the appropriate one. This is the "verify once, reuse everywhere" model working correctly — ensuring direct access to any service with a single set of verifiable credentials.
How do legacy systems integrate with modern verifiable credential infrastructure?
The recommended pattern is a credential bridge — a service that wraps the legacy system and issues W3C Verifiable Credentials on its behalf. The legacy system remains the source of truth. The bridge translates requests into the legacy system's protocol and wraps responses in standards-compliant digital credentials. The key risks are availability coupling and schema drift. This pattern is how regulated industries bridge existing legacy systems to modern credential infrastructure without service interruption.
What is the role of the World Wide Web Consortium in credential standards?
The World Wide Web Consortium (W3C) publishes the core specifications that define the data model, syntax, and verification rules for verifiable credentials and decentralized identifiers. The W3C VC Data Model and W3C DID Core specifications are the foundation on which interoperable credential systems are built. Compliance with these specifications ensures that credentials issued today can be verified by any compliant verification systems in the future — making them future-proof by design.
How does interoperability relate to fraud prevention and compliance audits?
A credential ecosystem built on standards-compliant trust registries is significantly more resistant to issuer impersonation — because every verifier independently validates that the issuer is authorised. Compliance audits benefit because standardised credential formats produce structured, machine-readable verification event records. An auditor can confirm what credential type was accepted, which issuer issued it, which schema version was used, and what the verification decision was — without any personal data in the audit trail.
Conclusion: Interoperability Is Not a Feature
Interoperability is not something you add to a credential system after it is built. It is the foundational commitment that determines whether your identity infrastructure is useful to anyone outside your own ecosystem.
A credential that only works with one verifier is a digital token, not a portable credential. An issuer whose credentials only one verifier accepts is a proprietary vendor, not a trusted authority in regulated industries.
The W3C standards stack — Verifiable Credentials, Decentralized Identifiers, selective disclosure, trust registries, and standardised interoperability protocols — exists precisely to prevent these outcomes. The teams that treat interoperability as a day-one architectural requirement are the ones whose users experience "verify once, reuse everywhere" as a reality rather than a promise.
Build for the credential ecosystem you want to participate in — not just the one that exists today.
What comes next. Once your credentials are portable and your verifiers are standards-compliant, the next operational challenge is proving every compliance decision to an auditor five years from now — without tracking users or storing any personal data. That is the subject of the next article in this series.
Next: Evidence Packs in Production: Logging That Proves Compliance Without Tracking Users (COMING SOON...)
Want to learn more?
Explore our other articles and stay up to date with the latest in zero-knowledge KYC and identity verification.
Browse all articles