
Key Management in Identity Systems: Rotation, Recovery, and Custody Compatibility
In production environments, cryptographic keys are not static assets. They move through a lifecycle shaped by security, recovery, and operational risk. Most architectures quietly assume identifiers are permanent, but institutional deployments update them on a regular schedule.
If a key rotation event breaks identity continuity or verifier trust, the deployment becomes dangerously brittle. The goal is to survive transitions without forcing unnecessary re-KYC or causing availability failures.
The 30-Second Map of the Key Lifecycle
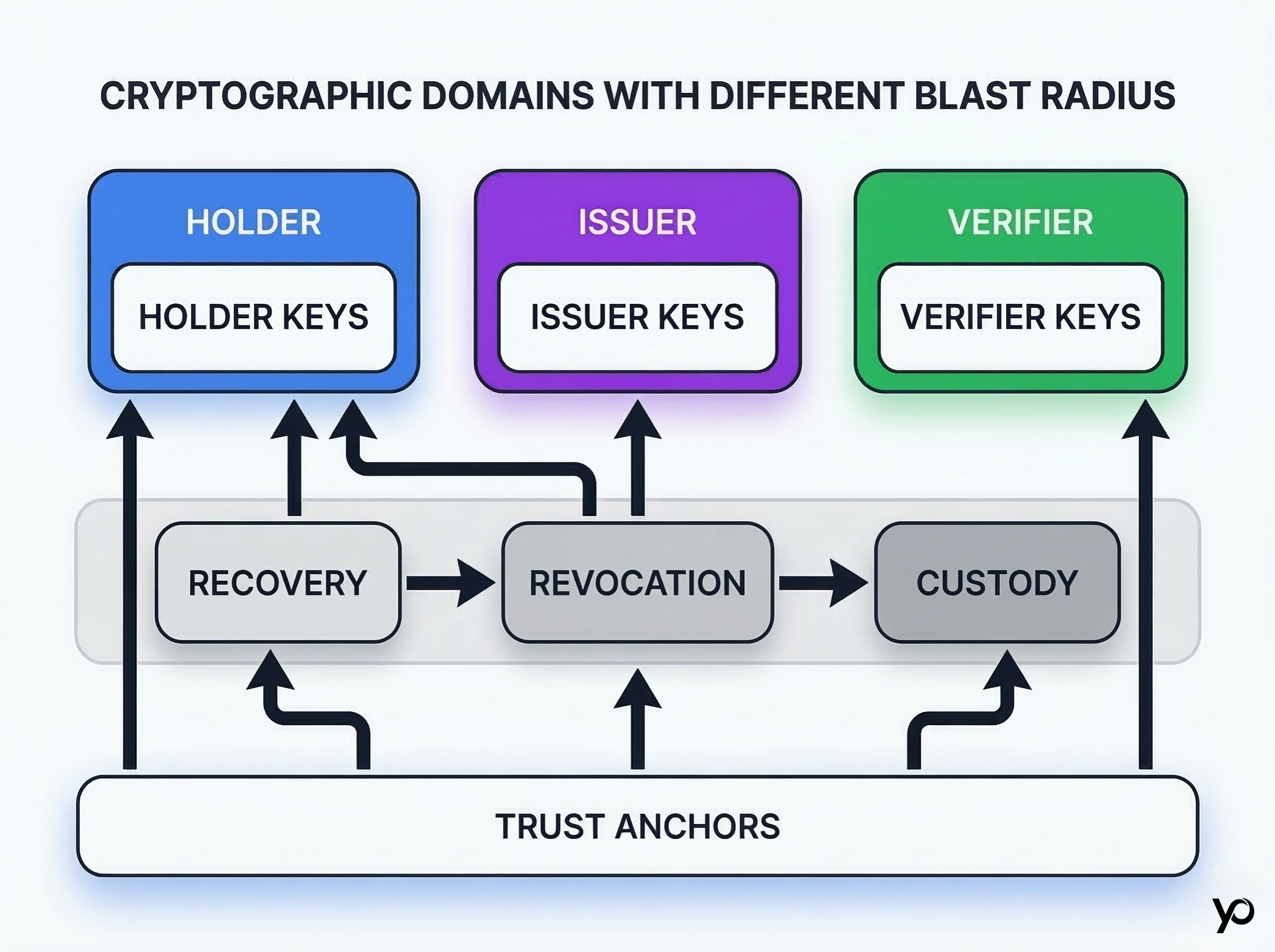
Holder keys, issuer keys, verifier keys. Identity architectures have multiple cryptographic domains, each with a different blast radius. Holders prove authority over data, issuers sign verifiable attestations, and verifiers authenticate requests. Each domain requires distinct handling.
Rotation, recovery, revocation, and custody are one operating system. These functions do not exist in isolation. The core secure process preserves continuity while changing the technical means of access. Changing a trust anchor in one domain usually requires an update elsewhere to maintain trust across various tokens and attestations.
Why key management fails in otherwise strong identity deployments
The “keys never change” assumption. Many protocols assume a public identifier is permanent. When hardware is lost, the user loses their entire history if the architecture lacks a continuity path [Citation: W3C Decentralized Identifiers (DIDs) v1.0 Core architecture regarding key recovery].
Availability failures vs security failures. A security breach happens when an attacker steals a secret. An availability failure happens when legitimate users are locked out because a recovery policy path is too rigid or a trust anchor was updated without notifying dependent services.
Why manual key rotation creates a fundamental risk
The best operational solutions reduce manual intervention during sensitive changes, because that is where avoidable risk usually enters the deployment. Relying on manual key rotation limits security and increases human error during critical transitions. Automation ensures execution remains consistent and safe.
Key rotation across the identity stack
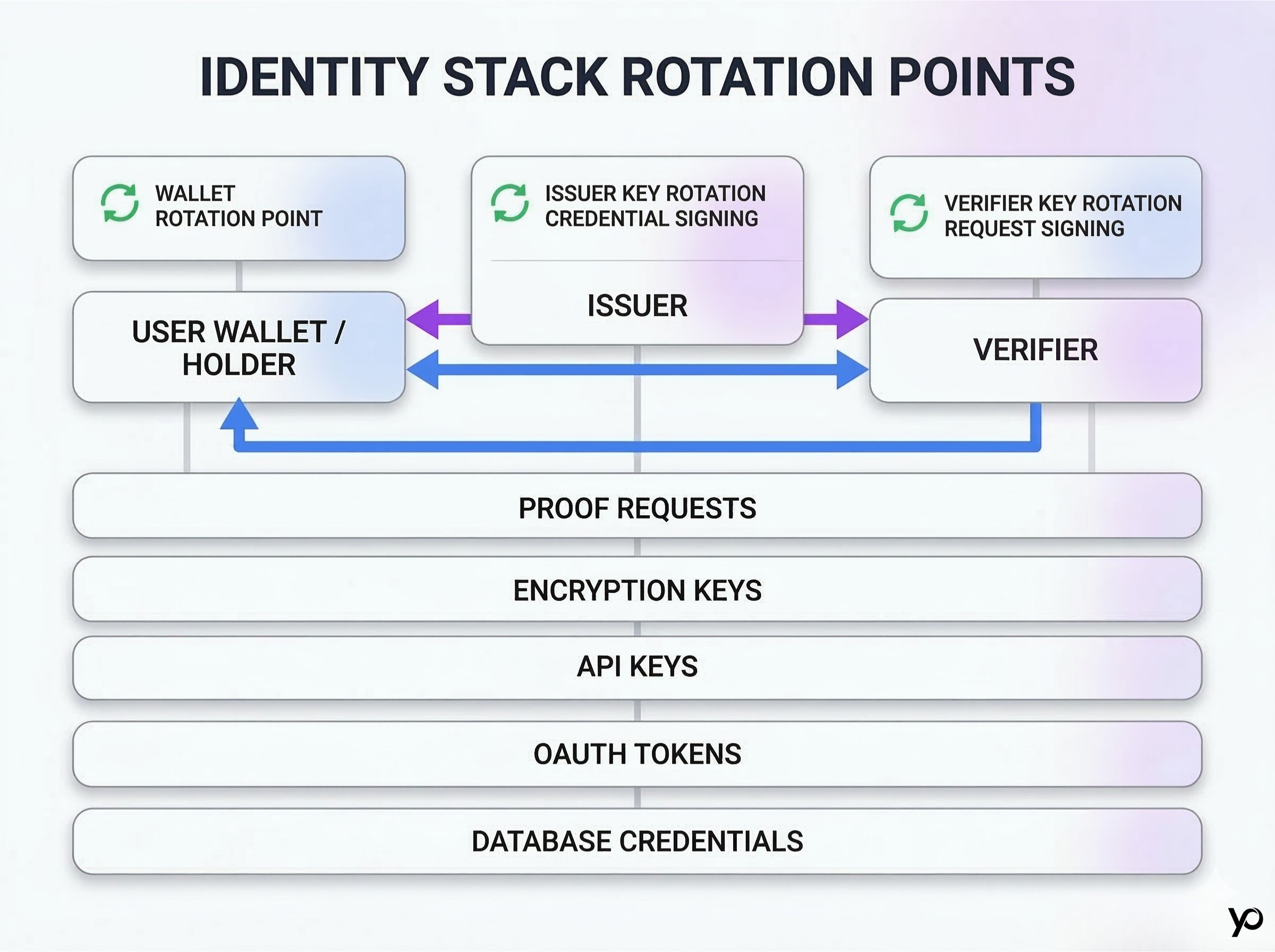
Wallet rotation for users and holders. When users upgrade devices, their wallet secrets must change with them. The framework must let them create a replacement signing pair and update their registry entry without discarding existing history.
Issuer key rotation for credential signing. Issuers must rotate their signing material proactively based on a schedule. Because thousands of active proofs rely on a single issuer, this key rotation requires careful overlap windows to prevent breaking valid attestations in the field.
Verifier key rotation for request signing and trust continuity. Verifiers must also update the material they use to request proofs. If compromised, an attacker could spoof verification requests to harvest sensitive information.
Encryption keys, API keys, and database credentials in the supporting stack. The surrounding stack matters too: poorly rotated encryption keys, API keys, OAuth tokens, or database credentials can expose sensitive data even when the core identity services are designed correctly. Data protection requires hardening both the trust anchors and the standard infrastructure supporting them on a regular schedule.
How to rotate a wallet without forcing full re-KYC
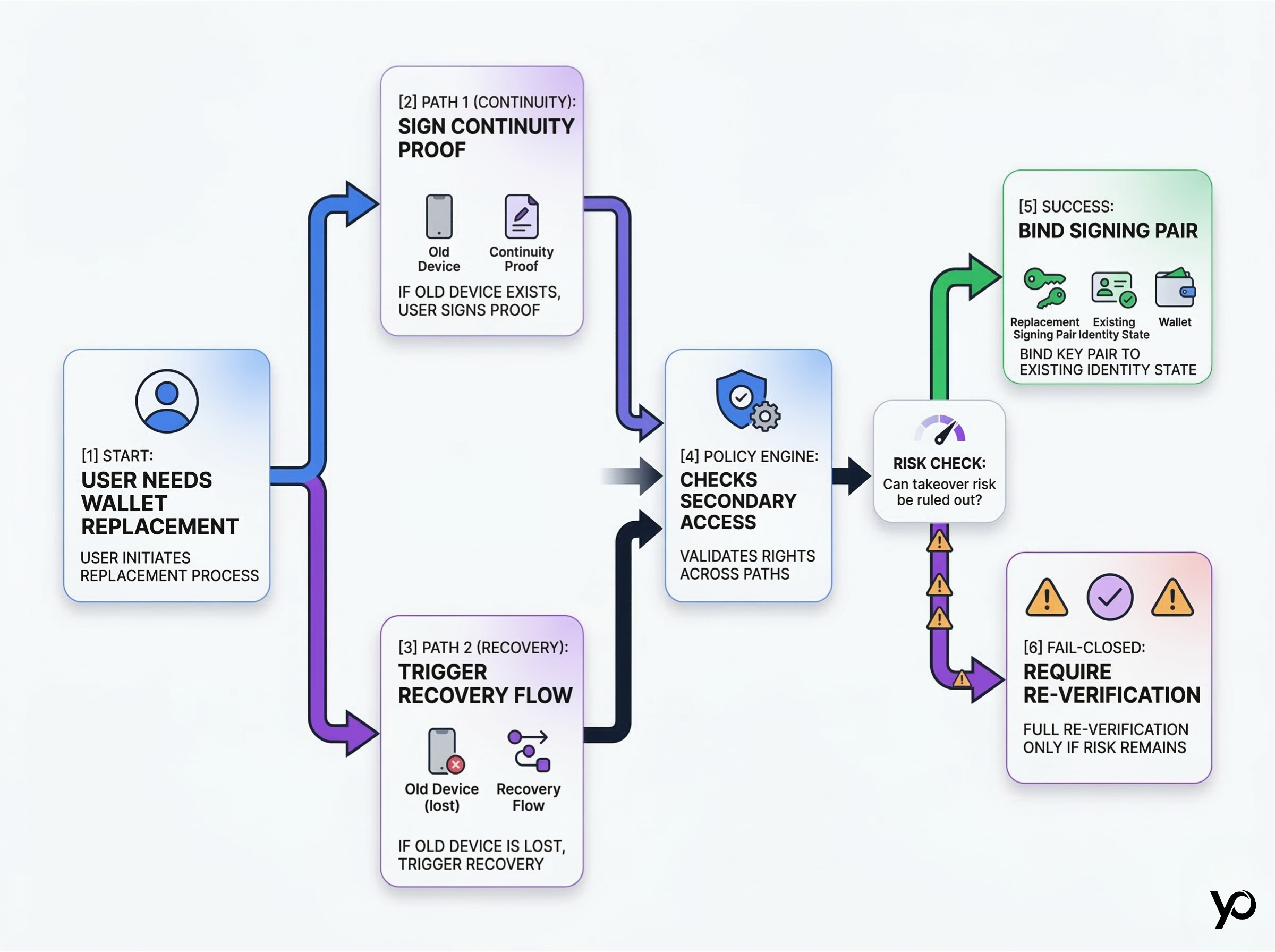
Continuity proofs and account binding. If a user retains access to their previous device, they can sign a cryptographic message authorizing the transition. This creates a continuity proof, binding the updated hardware to the existing state.
Recovery flows with policy checks. Good rotation policies separate identity continuity from the specific device or tokens currently used for access. If the previous device is lost, the architecture should rely on alternate recovery flows, verifying secondary access rights against a policy engine before authorizing the replacement signing pair.
When a full re-verification is actually necessary. Continuity should be the default, but full re-KYC is required if there is evidence of malicious account takeover. The network must fail closed when continuity cannot be cryptographically proven.
Key management in identity systems: rotation
Transitioning from the old key to the new key
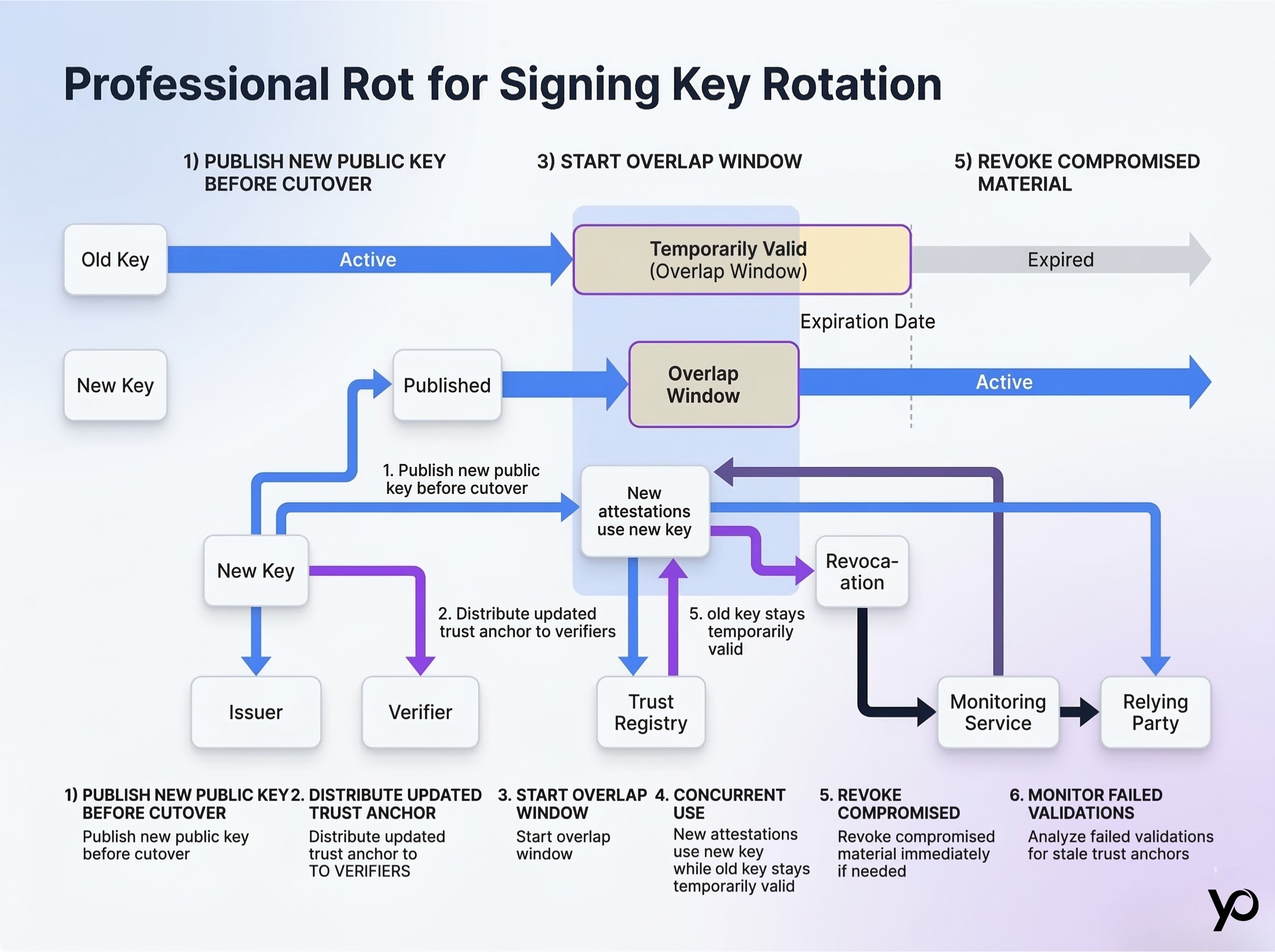
The most critical rule is to publish replacement signing material before the cutover occurs. To establish continuous trust, if an issuer begins signing before verifiers know the new key exists, incoming proofs will fail validation. The benefit of proper staging is zero downtime.
Overlap windows, expiration date, and revocation coordination. Safe transitions require an overlap schedule. The old key remains valid up to its hard expiration date, while the new key handles newly issued attestations. Under these circumstances, revocation coordination ensures compromised secrets are killed immediately. Never delete the old key until the overlap schedule concludes.
Monitoring for stale trust anchors. In practice, you must monitor services and dependent validation code closely. Failed validations often indicate that a relying party has hardcoded an outdated trust anchor and missed the key rotation event.
Custody arrangements for institutional architectures
Multi-sig and HSM-backed infrastructure. Institutions use Hardware Security Modules (HSMs) and multi-signature wallets to safeguard root secrets. Key rotation in these environments requires coordinated cryptographic ceremonies [Citation: NIST SP 800-57 Part 1 Rev. 5 for enterprise secrets management].
Delegated signing controls and access rights. A master root might issue temporary, narrowly scoped child secrets to automated services. This allows the operating model to update active signing pairs daily on a consistent schedule without touching the highly guarded root.
Separation of duties for secure operational control. In practice, institutional tools and custody solutions matter because the signing boundary is often split across hardware, policy, and approval workflows. The administrator approving the generation of a replacement should not be the one authorizing its deployment.
CTO Checklist for rotation, recovery, and custody compatibility
- Document the maintenance schedule for issuer, verifier, and infrastructure secret updates.
- Automation ensures you reduce manual error during scheduled rollover events.
- Define the exact cryptographic evidence required to recover an account without re-KYC.
- Test emergency revocation paths to ensure compromised signing material is invalidated globally in minutes.
- Determine which dependent services must refresh trust anchors before each transition.
Example 1 — User wallet rotation after device loss
For example, a user loses their smartphone and installs the wallet on a replacement device. They cannot use their old key to authorize the transition.
They initiate a recovery flow, providing a backup seed phrase or a biometric check against a secondary trusted service. Once the policy engine confirms those access rights, the workflow binds the replacement pair to the existing decentralized identifier, preserving compliance history without a frustrating re-KYC loop.
Example 2 — Issuer compromise and emergency rotation
An institution detects a breach on the server hosting its active credential signing service. They use their offline HSM to revoke the compromised material on the public trust registry immediately.
They generate a replacement signing pair and publish the updated public component. They then notify relying verifiers via automated webhooks that any proofs signed by the compromised material must be re-evaluated. The institution re-issues attestations to affected users using the successor.
Pitfalls, trade-offs, and anti-patterns
Treating recovery as a support issue instead of a security process. Wallet recovery is a core operating model, not a customer service ticket. If support agents can manually bind replacement pairs without strict cryptographic safeguards, social engineering attacks will compromise the deployment.
Letting revocation + key rotation become an availability nightmare. If revocation and key rotation are tightly coupled without graceful overlap windows, routine maintenance causes massive availability failures. Valid users get rejected because a verifier’s cache lagged behind the issuer’s transition.
Manual processes create avoidable failure points. Treating lifecycle events as ad-hoc tasks invites catastrophic mistakes. A manual process often leads to publishing the wrong public material or forgetting to update a dependent microservice.
Failing to communicate trust updates to dependent services. If an issuer rotates a secret but provides no programmatic way for verifiers to discover the change, the chain of trust breaks. Verifiers reject perfectly valid proofs against stale anchors.
What matters vs what is noise in key management
When evaluating an architecture, separate critical infrastructure needs from academic theory.
- Lifecycle thinking vs Static assumptions: Design networks assuming hardware will be lost, rather than treating public identifiers as permanent.
- Recoverable continuity vs Single-wallet dependency: Let users rotate wallets and keys while preserving history, instead of forcing re-KYC by default.
- Operational discipline vs reactive fixes: The best solutions define ownership, schedule, tools, and rollback steps before production incidents occur.
- Monitored key rotation vs Unmanaged secrets: Use automated tools to govern changes rather than relying on spreadsheets.
- Planned overlap vs Abrupt emergency cuts: Publish updates and update dependencies before deprecating old ones.
Conclusion
Identity deployments that survive production treat cryptographic material as living infrastructure, not fixed identifiers. The distinction between the human user and the tools they use to authenticate must remain absolute.
By designing for seamless key rotation, policy-driven recovery, and institutional custody arrangements, architects build deployments that adapt to security events without destroying user experience. A fundamental benefit is that trust remains continuous even when the underlying secrets inevitably change.
FAQ
What is key rotation in identity systems?
It is the scheduled or emergency process of replacing active signing material after expiry, compromise, or policy-driven rollover. This limits the volume of data signed by a single source, reducing the impact of a potential compromise.
When should a user wallet be rotated?
A user wallet should undergo key rotation when a device is lost, sold, or suspected of being compromised.
Does wallet recovery always require full KYC again?
No. If the architecture is designed correctly, a user can authenticate via secondary methods to bind replacement signing material to their existing verified profile.
How do issuer keys and verifier keys differ?
Issuer cryptographic keys sign verifiable attestations, acting as the root of trust. Verifier keys authenticate requests for proofs and validate the responses provided by users.
What role do custody arrangements play in identity systems?
They determine how institutional cryptographic keys are safeguarded and governed. They involve HSMs and multi-signature policies to ensure highly sensitive material cannot be misused by a single administrator.
How do revocation and key rotation interact?
Key rotation is a planned transition to successor material. Revocation is immediate invalidation, usually due to compromise. A well-scoped workflow coordinates both safely. In practice, this is essential for services that rely on cached trust anchors or short-lived tokens.
Can automatic rotation reduce human error?
Yes. Automatic rotation for infrastructure secrets significantly limits exposure by removing manual intervention, which is the leading cause of misconfigurations.
How do we maintain data protection for supporting infrastructure?
Strong data protection requires updating API keys, encryption keys, and database credentials on a strict schedule just as rigorously as the core identity cryptographic keys to prevent lateral breaches.
What Comes Next
Understanding how cryptographic keys transition safely is only half the battle. Once your identity architecture is live in production, the deployment must be able to survive infrastructure outages, latency spikes, and oracle failures without halting your entire business.
Production Operations: Monitoring, SLAs, and “Fail-Closed” Without Bricking Your App
Want to learn more?
Explore our other articles and stay up to date with the latest in zero-knowledge KYC and identity verification.
Browse all articles